Содержание
- Understanding And Leveraging The Csf
- Phase Ii Hitrust Validated Assessment
- Hitrust Csf
- Sidetrade Predicts Payment Behavior To Provide Better Customer Service
- Saudi Arabian Monetary Authority Sama Cybersecurity Framework
- New Zealand Protective Security Requirements Psr
- European Union Agency For Cybersecurity Enisa National Capabilities Assessment Framework
Based on the answers to these questions, they will better understand which of the benefits presented in this article will apply to their organization should they implement the Framework. Prepare for security events – Prepare for an incident by having incident management and investigation policy and processes that align to your organizational requirements. Run incident response simulations and use tools with automation to increase your speed for detection, investigation, and recovery.
Together these technologies detect weak signals and predict risks by rapidly analyzing massive amounts of data – so you can react to suspicious behaviors immediately. The ideas with prescriptive security are very relative to those we’ve already been trying to implement as part of a responsible cybersecurity program such as documentation, process and procedures, handbooks, and even checklists. LEaders also know the business better than the cybersecurity professional and can get us information and solutions that we couldn’t achieve on our own. Many times, the unknowns we struggle with are a business question and they can solve it. They also have the ability to go and get the additional funding for resources, whether technology or labor, to help us address those unknowns. And whether those unknowns are figured out and secured or not, the business deserves to know about them.
Understanding And Leveraging The Csf
Enable traceability – Monitor, generate alerts, and audit actions and changes to your environment in real time. Integrate log and metric collection with systems to automatically investigate and take action. The ISF is a no-profit organization whose members consist of companies on the Fortune 500 and Forbes 2000 lists.
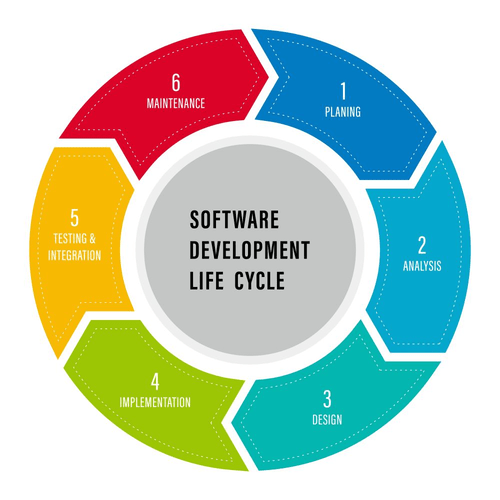
An accurate cyber risk calculation needs to consider 5 factors as show in Fig 3. These events add to the many recent instances of hacking of bank and other private companies’ IT systems. The first stage involves assessing your processes and the tools you currently use to give you a clear picture of where you are today in comparison with where you need to be.
The FedRAMP Program Management Office mission is to promote the adoption of secure cloud services across the Federal Government by providing a standardized approach to security and risk assessment. The PSPF is applied through a security risk management approach with a focus on fostering a positive culture of security within an entity and across the government. During the first stage you should have assessed your processes and tools, have a clear picture of where you need to be, detected any gaps and defined an action plan.
Suppose you are the chief executive officer of an airline and you want to maximize your company’s profits. Prescriptive analytics can help you do this by automatically adjusting ticket prices and availability based on numerous factors, including customer demand, weather, and gasoline prices. It can also be used to analyze which hospital patients have the highest risk of re-admission so that health care providers can do more, via patient education and doctor follow-up to stave off constant returns to the hospital or emergency room. Prescriptive Security with its advanced algorithms can quickly identify any suspicious behavior, triggering remediation actions for eliminating threats without delay. The real-time changes aimed at avoiding breaches might block attempts to take a screenshot of data, to copy data to a removable device or to send it to a Dropbox account, for example.
Phase Ii Hitrust Validated Assessment
The following post comes to us from Paul A. Ferrillo, counsel at Weil, Gotshal & Manges LLP specializing in complex securities and business litigation, and is based on an article authored by Mr. Ferrillo and Tom Conkle. Implement a strong identity foundation – Implement the principle of least privilege, and enforce separation of duties with appropriate authorization for each interaction with your AWS resources. Centralize identity management, and aim to eliminate reliance on long-term static credentials.

Digital is opening up new opportunities for cybercriminals and cyberattacks are growing in scale, complexity and frequency. Criminals also engage in everything from money laundering to violating trade embargos, as well as exploiting the complex and unstable world of international regulations to conduct ‘grey zone’ transactions. Security analysts are all different, and based on talent and abilities can have very different approaches and communicate different priorities. We’re a signer of the Climate Pledge and a contributor to the UN’s Race to Zero initiative. And in 2020 we acquired EcoAct, an internationally recognized climate strategy consulting firm.
Additionally, directors should have a deep discussion with management about the organization’s Implementation Tiers. The Implementation Tiers allow an organization to consider current risk management practices, the threat environment, legal and regulatory requirements, business/mission objectives, and organizational https://globalcloudteam.com/ constraints. The diagram above provides questions to help determine if and how an organization can benefit from implementing the Framework. Discussing these questions and their responses will help organizations determine how well their current cybersecurity efforts are protecting them against cyber attacks.
Hitrust Csf
Implementing the Framework will not only allow organizations to improve cyber security measures, but also to effectively demonstrate due care. The Well-Architected security pillar describes how to take advantage of cloud technologies to help protect data, systems, and assets in a way that can improve your security posture. This will help you meet your business and regulatory requirements by following current AWS recommendations.

This EU data protection framework aims to address new challenges brought by the digital age. It enforces rules on how organizations collect, process and protect customers’ information. Even though these questions offer a repeatable set of things to consider so that the proper security procedures can be initiated, it’s still not the heart of prescriptive security. Where it really gets traction is in the ‘Protect’ section of the NIST framework.
Sidetrade Predicts Payment Behavior To Provide Better Customer Service
For example, HITRUST is one vehicle for meeting HIPAA compliance, but it’s not a requirement, and SOC 2 can be used as a vehicle for demonstrating GLBA compliance. AICPA Trust Services Principles and Criteria is a holistic set of standards that is utilized in SOC 2 and SOC 3 engagements. It is a set of five information integrity standards focusing each on Security, Availability, Confidentiality, Processing Integrity and Privacy.
- The organization focuses on creating a knowledge exchange where members share security issues, experiences, and practical solutions.
- Educating managers and staff on the Framework to ensure all organizations are on the same page is also an important step toward the successful implementation of a robust cybersecurity program.
- As a single suite of data integration and data integrity applications, Talend Data Fabric is the quickest way to acquire trusted data for all of your reports, forecasting, and prescriptive modeling.
- These analytics go beyond descriptive and predictive analytics by recommending one or more possible courses of action.
- But attack surfaces have increased, making finding those needles – that increasing number of intrusions – almost impossible.
- Prescriptive analytics can help you do this by automatically adjusting ticket prices and availability based on numerous factors, including customer demand, weather, and gasoline prices.
Amidst the COVID-19 crisis, the network security industry is poised for sustainable growth despite the foreseeable economic turbulence. Implementation of remote working policy, due to lockdown is putting unanticipated stress on remote networking technologies and causing operational technology security risk concerns over the vulnerable home network security. Prescriptive analytics is a form of data analytics that helps businesses make better and more informed decisions. Its goal is to help answer questions about what should be done to make something happen in the future.
Many companies outside of the critical infrastructure industry also use the CSF, especially if they need to meet other US federal data protection requirements. The Red Flags Rule establishes new provisions within FACTA requiring financial institutions, creditors, etc. to develop and implement an identity theft prevention program. An existing Nevada statute relating to personal information collected by governmental agencies requires the state data collectors to implement and Understanding Prescriptive Security maintain “reasonable security measures” to protect such records. CIS Critical Security Controls – Prescriptive, prioritized, and simplified set of cybersecurity best practices. CIS’s cybersecurity best practices and tools can assist organizations who are working towards compliance. The HITRUST Common Security Framework was developed in collaboration with healthcare and information security professionals to provide a prescriptive framework to simplify security requirements.
Saudi Arabian Monetary Authority Sama Cybersecurity Framework
Educating managers and staff on the Framework to ensure all organizations are on the same page is also an important step toward the successful implementation of a robust cybersecurity program. The previously mentioned CForum is a source for success stories, lessons learned, questions and information useful to organizations implementing the Framework. This information about existing Framework Implementations may help organizations with their own approaches. Additionally, organizations can seek out cybersecurity service providers skilled in helping organizations with the education, awareness and planning required to implement the Framework across an entire enterprise. NIST is a US non-regulatory government agency that sets standards across the physical sciences. Originally intended for critical infrastructure owners and operators, NIST CSF can be used by any organization.
This standard is frequently requested by financial institutions and publicly traded entities in order to comply with the GLBA and SOX legislation, although neither federal acts directly require them. Keep people away from data – Use mechanisms and tools to reduce or eliminate the need to directly access or manually process data. This reduces the risk of mishandling or modification and human error when handling sensitive data. Data protection to maintain visibility and control over data, and how it is accessed and used in your organization. Critical Infrastructure Protection is just one of 14 mandatory North American Electric Reliability Corporation security frameworks that are subject to enforcement in the U.S. The IASME Governance standard was developed over several years during a government funded project to create a cyber security standard which would be an affordable and achievable alternative to the international standard, ISO 27001.
In May 2017, the Saudi Arabian Monetary Authority issued Version 1.0 of its Cyber Security Framework . In the introduction, SAMA noted that applying new online services and new developments, such as fintech, and blockchain, require additional regulatory standards to protect against continuously evolving threats. OASIS Open is a community where experts can advance projects, including open source projects, for cybersecurity, blockchain, IoT, emergency management, cloud computing, and legal data exchange. The United Kingdom’s NCSC launched in 2016 and brings together SMEs, enterprise organizations, government agencies, the general public, and departments to address cybersecurity concerns. Ultimately, COBIT’s focus on governance creates a security framework that streamlines audits and incorporates continuous improvement to enhance those outcomes. Within each domain, CCM lists controls and specifications to help organizations create a compliant security program.
This security framework publication presents a new conceptual framework for providing information technology security training. This framework includes the IT security training requirements appropriate for today’s distributed computing environment and provides flexibility for extension to accommodate future technologies and the related risk management decisions. Control Objectives for Information and Related Technology is a security framework created by ISACA for information technology management and governance.
The guidance and best practices provided by the framework help you build a comprehensive approach to cloud computing across your enterprise and throughout your IT lifecycle. Each perspective covers distinct responsibilities owned or managed by functionally related stakeholders. In general, the business, people, and governance perspectives focus on business capabilities; whereas the platform, security, and operations perspectives focus on technical capabilities. Using SecurityScorecard, organizations can align their security controls with our ten categories of risk. Since Atlas maps to over 20 industry-standards, organizations can create a holistic, automated compliance program and remove the human error risk that comes from using spreadsheets. The Definitive Guide to Security Posture will cover what is security posture, how you can assess and improve your enterprise security posture.
Under each of the 20 controls, the CIS Controls framework provides a list of sub-controls, color-coded to indicate which implementation group should be using them. For example, CIS Control 1 “Inventory and Control of Hardware Assets” lists sub-control “Utilize an Active Discovery Tool” is appropriate for Implementation Groups 2 and 3 but considered too much of a burden for Group 1. The Information Security Registered Assessors Program is an Australian Signals Directorate initiative to provide high-quality information and communications technology security assessment services to government. The Protective Security Policy Framework is a security framework that assists Australian Government entities to protect their people, information and assets, both at home and overseas. Business intelligence refers to the procedural and technical infrastructure that collects, stores, and analyzes data produced by a company. Prescriptive analytics isn’t foolproof, as it’s only as effective as its inputs.
With our all-in-one solution, organizations can monitor their own infrastructure and build out a robust vendor risk management program for a proactive approach to cybersecurity and compliance. Founded in 1945, ISA is a non-profit professional association that established a Global Security Alliance to work with manufacturers and critical infrastructure providers. GSA incorporates various stakeholders, including end-user companies, automation and control systems providers, IT infrastructure providers, services providers, and system integrators. The Information Systems Audit and Control Association updated its COBIT framework in 2019 to create a Governance System and Governance Framework. Instead of basing compliance on individual security controls, COBIT 2019 starts with stakeholders’ needs, assigns job-related governance responsibilities to each type, then maps the responsibility back to technologies. Ultimately, COBIT’s goal is to ensure appropriate oversight of the organization’s security posture.